
Celestix Networks, Inc.
Americas: +1 510 668 0700
EMEA : +44 20 3900 3737
Asia : +65 6958 0822
Japan : +81 3 5210 2991
Protect accounts from identity theft with multi-factor authentication backing your Zero Trust Solutions.
Single tap push notification approval. Simplified authentication and one tap login, straight from your mobile device, with InstaSafe Authenticator App.
Extend adaptive Multi-Factor Authentication to all your users. Reinforce your Zero Trust model with secure single sign on to all applications.
Seamlessly manage complex access requests for employees that work outside the office.
Put a lid on all weak passwords using multi-factor authentication that leverages passwordless authentication.
Strengthen your Zero trust Secure Access stack with an additional layer of inbuilt Multi-Factor Authentication capability that supports your IAM infrastructure.
Web Apps MFA
InstaSafe provides additional factor authentication for web applications and email clients that support SAML or RADIUS authentication protocols. InstaSafe supports integrations with popular applications including O365, Zoho, Salesforce, Gitlab, Atlassian; and popular email clients including Zimbra, ICEWrap, Microsoft Office 365/ Exchange.
Protocols Support
SAML, OAuth, OpenID Connect.
Authentication Methods
OTP, T-OTP, MPIN, Biometrics, Push notification, Hardware Token
Compliance
PCI DSS, HIPAA, GDPR, SOX.
Desktop MFA
With the InstaSafe MFA, users will be prompted to provide a secondary factor of authentication along with the password while doing a login to their Windows/ Linux/ MAC system. MFA can also be enabled for RDP services.
Operating System Supported
Windows, Linux, Mac.
Protocols Support
RADIUS, LDAP, Active Directory (Kerberos), SSH, Open Directory.
Authentication Methods
OTP, T-OTP, MPIN, Biometrics, Push notification, Hardware Token.
Compliance
PCI DSS, HIPAA, GDPR, SOX.
Network MFA
InstaSafe supports MFA for VPN, firewall, router, switches and other network devices using RADIUS and TACACS authentication protocols.
MFA for ADFS and LDAP
InstaSafe supports MFA for popular directory services including ADFS and LDAP and reduce the risk of data breaches and unauthorized access.
InstaSafe provides additional factor authentication for web applications and email clients that support SAML or RADIUS authentication protocols. InstaSafe supports integrations with popular applications including O365, Zoho, Salesforce, Gitlab, Atlassian; and popular email clients including Zimbra, ICEWrap, Microsoft Office 365/ Exchange.
Protocols Support
SAML, OAuth, OpenID Connect.
Authentication Methods
OTP, T-OTP, MPIN, Biometrics, Push notification, Hardware Token
Compliance
PCI DSS, HIPAA, GDPR, SOX.
With the InstaSafe MFA, users will be prompted to provide a secondary factor of authentication along with the password while doing a login to their Windows/ Linux/ MAC system. MFA can also be enabled for RDP services.
Operating System Supported
Windows, Linux, Mac.
Protocols Support
RADIUS, LDAP, Active Directory (Kerberos), SSH, Open Directory.
Authentication Methods
OTP, T-OTP, MPIN, Biometrics, Push notification, Hardware Token.
Compliance
PCI DSS, HIPAA, GDPR, SOX.
InstaSafe supports MFA for VPN, firewall, router, switches and other network devices using RADIUS and TACACS authentication protocols.
InstaSafe supports MFA for popular directory services including ADFS and LDAP and reduce the risk of data breaches and unauthorized access.
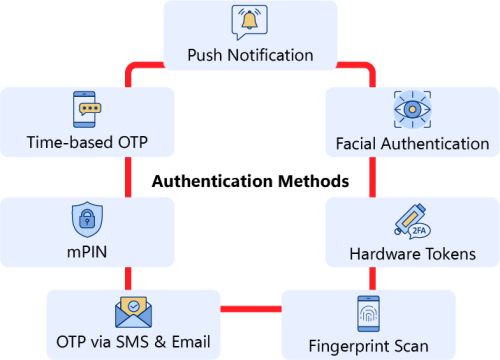
The most used type of MFA is biometric verification, which includes fingerprint scan, retinal scan, voice recognition, etc. Users who have access to smartphones and laptops can implement this biometric authentication to strengthen their securityeasures. To implement biometric verification, users at the time of registration need to provide their fingerprint and facial scan. The system will store the information, and whenever the user accesses the device using face recognition or fingerprint, the access will be granted.
Another important MFA example is phone authentication using time-based OTPs sent to the registered number or email. It is generally a six-digit number code that is only valid for a limited period. To incorporate phone authentication, users need to provide the number and enable multi-factor authentication at the time of registration. So whenever a user accesses the account using credentials, an OTP will be sent. After entering the OTP, access will be granted.
Another robust authentication type is the use of hardware tokens. These hardware tokens can be security keys or tokens which are in the user's possession. Whenever the user tries to access sensitive resources or data, applications or networks using credentials, a security key in their possession needs to be inserted into the device. This MFA authentication type is generally expensive compared to other methods and is usually employed by businesses that are ready to go the extra mile for security.
Software token authentication is another type of MFA. In this authentication mechanism, mobile devices or authentication applications have been used to grant access. The organization needs to tie up with third-party authentication applications to grant access to their network. Since there is no need to carry any additional device like security keys, etc, this type of authentication mechanism is widely popular.
InstaSafe Authenticator can integrate with any VPN or remote gateway.
Compatible with any FIDO compliant security hardware key.
It supports RADIUS, TACACS, OAUTH and SAML Authentication protocols.
Mobile app with various authentication methods available.
User can get authenticated to the application using their live face. Continuous facial authentication further checks the liveness of the user by monitoring the face every 30secs. If the user moves out from the frame of device screen or any third person comes infront of the device screen, the application gets automated logged out. This authentication mechanism is helpful for very sensitive business applications.
FIDO (Fast Identity Online) is an Open and standardized authentication protocols developed by FIDO alliance aims to eliminate the password problem of authentication and Man in the middle attack associated with MFA hacking. FIDO authentication is based on public key crytography. FIDO allows users to sign in using passkeys. Passkeys are stored locally on the devices with the biometric information.
RADIUS is a client-server networking protocol that enables centralized authentication and authorization for a remote network. InstaSafe controller can act as a RADIUS server while prompting for MFA. Radius supports a variety of authentication methods, including PAP (Password Authentication Protocol), CHAP (Challenge Handshake Authentication Protocol), EAP (Extensible Authentication Protocol), and more.
TACACS is a network security protocol that provides centralized authentication, authorization, and accounting services to access network devices and services. TACACS provide additional security feature compared to RADIUS as it uses a separate encryption key for each services. TACACS is associated with CISCO networking equipment and used to secure access to CISCO devices. InstaSafe controller can act as a TACACS server and enable authentication.
Windows Login is a simplified, secure authentication solution that improves the logon security of Windows Desktops, Servers, and Windows Terminal Servers, ensuring a secure login experience for your users. InstaSafe Authenticator can improve security posture by adding an additional factor of authentication when logging into Windows systems.
When it comes to MFA vs 2FA, 2FA requires only one additional security measure other than username and password. While MFA requires more than one security mechanism other than username and password. Based on the mechanism, MFA is considered more secure than two-factor authentication. Not just this, there are various two-factor authentication risks, such as phishing attacks, stolen devices, social engineering, etc.
The primary purpose of MFA is to add an extra layer of protection beyond just passwords, mitigating various threats. There are various risks of not having an MFA, such as credential theft, compliance concerns, insider threats, etc.
There are three main categories of authentication methods: something you know (e.g., password), something you have (e.g., security token), and something you are (e.g., biometric data).
Common MFA methods include using a password and security token, using a password and biometrics (e.g., fingerprint), using SMS codes, and using an authenticator app.
While no security method is completely foolproof, MFA significantly reduces the risk of hacking by requiring multiple layers of authentication. However, it is important to use strong and unique passwords, keep software and devices up-to-date, and be cautious of phishing attacks.
Multi factor authentication can be powered by various solutions and methods. The method can be password based or passwordless. Most prominent methods are mobile applications and the SMS, Email powered Time-based One-Time Password Authentication.
MFA comes inbuilt at ZTA. the MFA can be enabled and configured for users at the Controller Admin portal. The controller will force the user for an MFA based on the user configurations.
Many times, an external user wins over an authentication making use of various hacking methodologies such as bruteforce or Zero day exploits. Having an additional authentication will protect the applications and access by an additional layer of checks and security.
InstaSafe integrates seamlessly with every internal applications, databases, and cloud



Celestix Instasafe MFA, powered by the Authenticator Application supports and complements InstaSafe’s other Zero trust capabilities

Celestix Networks, Inc.
Americas: +1 510 668 0700
EMEA : +44 20 3900 3737
Asia : +65 6958 0822
Japan : +81 3 5210 2991