V-Key Multi-Factor Authentication
A Digital Trusted Platform for Authenticating Identities Worldwide

ONE-TAP LOGIN
SECURITY
Enjoy ultimate Security and peace of mind with our patented V-OS technology
ONE APP FOR ALL
INSTANT BACKUP AND RESTORE
2FA data backup in the Cloud. Easily restore your data when you switch to a new phone
Enterprise MFA solutions are not created equal
Strong authentication is essential in the digital age. Not all Multi-factor authentication solutions are equal, so deploying any solution is a myth.
Passwords alone aren't sufficient for secure access. MFA add protection through multiple factors, but some combinations may not be secure if they rely on easily compromised factors like passwords.
Protect Your Windows Devices
V-Key MFA for Windows Logon, an extension of V-Key Smart Authenticator, is designed to enhance security on Windows devices by integrating Multi-Factor Authentication (MFA) into the logon process. It ensures that only authorized individuals can access critical resources while also safeguarding desktop applications and processes.
This solution delivers a secure and seamless logon experience for Windows users, reinforcing the overall security framework.
Unparalleled Security
V-Key Multi-factor authentication offers highly secure authentication without relying on passwords, which reduces the risk of password-related vulnerabilities. The passwordless access system eliminates the possibility of password-related issues and significantly strengthens system security against unauthorized access.
Unique Security Features
V-OS provides an isolated environment to protect keys. It is a layer between the device operating system and V-Key. Protection from brute force attacks.
With V-OS Virtual Secure Element, it is resistant to attacks, including Trust Gap
V-OS Threat Intelligence (v4.8+) identifies security insights data visualization and provides a prediction model of which devices are under attack
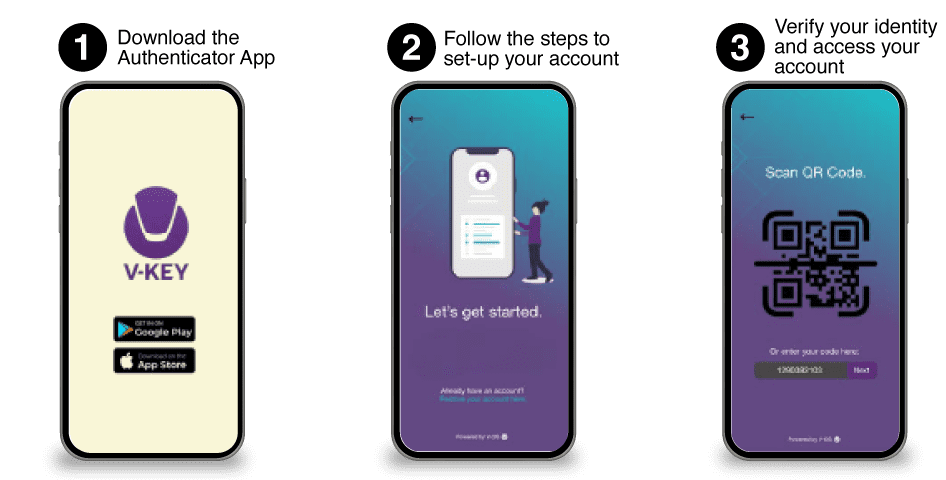
Provide Enterprise-Grade Multi-Factor Authentication in 3 EASY STEPS
Businesses, like relationships, are built on trust. Are your employees working remotely? Do you have a large number of users who need to access your app or system? With organizations moving towards Multi-Factor Authentication, a simple password is just not enough. NIST deprecated SMS OTP many years ago as they are vulnerable to interception and phishing attacks. Hardware tokens are expensive to deploy, can get lost or stolen, are not user-friendly, and require regular replacement. Turn your phone into a hardware token with the V-Key Smart Authenticator with industry-strength Multi-Factor Authentication that is tailored to scale for small and medium-sized businesses.
Use Cases

Enhance RADIUS or Active Directory or Entra ID

Cloud-based Services Authentication
Passwordless Login
Secure Windows PCs

Secure VPN access
Secure VDI Access

Secure Remote Desktop

RDS Authentication
V-Key MFA Product Brief

Safeguard Hybrid IT Environments.
Your business is probably comprised of an intricate combination of managed and BYOD machines, which access cloud, on-premises, and legacy resources. While numerous MFA platforms excel in providing security for their own range of products, they often lack compatibility with other systems. This inadequacy poses a threat to your security. In contrast, V-Key is designed to seamlessly integrate with various platforms, ensuring a unified front for your security measures.
Secure the Remote Workforce
V-Key multi-factor authentication solution ensures secure remote work by using Threat Intelligence to evaluate each login request and implement supplementary verification measures if needed. With V-Key, enterprises can trust the security and reliability of their valuable information.
Lower Your Total Cost of Ownership
Not all Enterprise MFA solutions are equal. V-Key allows for swift implementation and independent end-user enrollment, saving valuable time and money. Automated threat analysis and compliance reports allow IT and security teams to stay ahead of potential threats.
Connectors & Protocols
SAML
SAML provides a single, unified digital identity across every application and website. Centralised authentication assures IT admins of a single point of contact for all
RADIUS
RADIUS minimises the chances of hackers accessing an organisation’s data through networks (e.g WiFi) as it provides unique credentials for individual users.
OIDC
OIDC puts personal information under user control instead of by a service provider or other third party. Users can determine how personal info to share with other websites that use OIDC.

Obtain High-quality VPN Security with V-Key
Looking to protect SharePoint portals? remote access via Citrix XenDesktop? Firewall access? V-Key works in all of these scenarios. V-Key MFA is a simple and easy-to-deploy multi-factor authentication solution that uses your phone as a token. V-Key authentication service hosted in the cloud with a pay-as-you-go price model.
How Important is VPN Protection?
Looking to protect SharePoint portals? remote access via Citrix XenDesktop? Firewall access? V-Key works in all of these scenarios. V-Key MFA is a simple and easy-to-deploy multi-factor authentication solution that uses your phone as a token. V-Key authentication service hosted in the cloud with a pay-as-you-go price model.
Strengthen your VPN security with extra protection.
V-Key Technology Overview White Paper
Download NowSecure cloud accounts from credential theft and fraud with V-Key
Ensure the safeguarding of your accounts and applications by implementing a robust multi-factor authentication system, effectively permitting authorized individuals while preventing unauthorized access. Safeguard all valuable assets, encompassing customer-oriented and enterprise applications that house highly confidential information.
Selected Applications